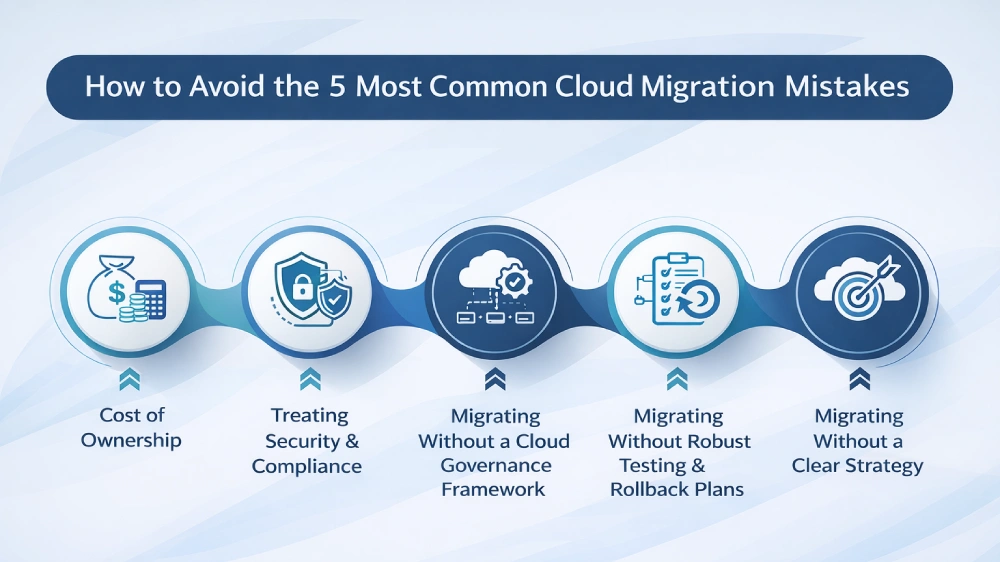
How to Avoid the 5 Most Common Cloud Migration Mistakes
Organizations that rush into the cloud without a disciplined strategy spend 30-40% more than budgeted - and still miss deadlines. Here's what separates successful migrations from expensive cautionary tales.
Cloud migration is not an IT project. It is a business transformation - and the organizations that treat it as anything less are the ones that end up replatforming the same workloads twice.
IN THIS ARTICLE
- 1. Lifting & Shifting Without Optimization
- 2. Underestimating Total Cost of Ownership
- 3. Neglecting Security & Compliance Early
- 4. No Clear Governance Framework
- 5. Migrating Without Testing & Rollback Plans
According to Gartner, through 2026, more than 90% of enterprises will use a multi-cloud architecture - yet a disproportionate share of those migrations will generate regret. Not because the cloud doesn't deliver on its promise, but because the path to value is riddled with well-documented, entirely avoidable pitfalls.
The five mistakes below are not theoretical. They are the recurring patterns that cloud architects, finance teams, and CIOs encounter again and again. Each one has a data signature, a root cause, and - critically - a proven countermeasure.
1 Lifting & Shifting Without Optimization
The lift-and-shift approach - moving workloads to the cloud with minimal modification - is seductive because it appears fast. In practice, it trades short-term speed for long-term structural debt. On-premises workloads are typically designed to run on hardware that is always on, with fixed capacity provisioned for peak load. In the cloud, that design pattern translates directly into overprovisioned, underutilized instances that bill 24/7.
The cost reality: IDC research indicates that organizations running lift-and-shift migrations often overprovision cloud resources by 35-45%, paying for capacity they never use - particularly in compute-heavy environments with uneven demand patterns.
The deeper problem is architectural. Applications designed for monolithic, on-premises architectures often cannot take advantage of cloud-native capabilities - auto-scaling, managed services, serverless functions - without refactoring. A lift-and-shift migration does not unlock the cloud's economic model; it merely relocates legacy costs to a new billing environment.
The fix: Conduct a workload rationalization exercise before migration. Classify each application using the 6R framework - Retire, Retain, Rehost, Replatform, Refactor, Repurchase - and prioritize replatforming for workloads with variable demand profiles. Right-sizing analysis tools should inform instance selection from day one, not after the first invoice arrives.
Action checklist
- Map peak vs average CPU/memory utilization for each workload pre-migration
- Identify applications that would benefit from managed database or serverless tiers
- Set a right-sizing review cadence within 30 days of go-live
- Apply Reserved Instance or Committed Use Discount pricing for stable, predictable workloads
2 Underestimating Total Cost of Ownership
Cloud pricing is deceptively complex. Decision-makers who evaluate cloud cost based solely on compute instances routinely miss the components that drive the largest unexpected bills: egress fees, API request charges, inter-region data transfer, licensing uplift for third-party software, and the operational overhead of managing a distributed cloud environment.
The budget gap: A Flexera State of the Cloud report found that organizations waste an average of 28% of their cloud spend annually - the majority attributable to oversized resources, unused reservations, and orphaned storage - while simultaneously underbudgeting for egress and observability tooling.
"If your cloud business case doesn't include egress costs and a licensing audit, it isn't a business case. It's a partial forecast."
One of the most underappreciated TCO components is the people cost. Cloud environments require ongoing management: cost governance, security posture reviews, capacity planning, and incident response. Organizations that staff cloud teams at pre-cloud levels frequently discover that operational expenses erode the savings the migration was supposed to generate.
The fix: Build a comprehensive TCO model before signing any cloud contract. Include compute, storage, network egress, third-party licensing, observability, security tooling, and a loaded cost for internal FTE work. Establish a FinOps practice - even a lightweight one - on day one. Cloud cost management is not a finance function; it is an engineering discipline.
TCO - What's commonly missed
| Cost Category | Commonly Included? | Frequently Missed? |
|---|---|---|
| Compute (EC2, VMs) | Yes | - |
| Object storage | Yes | - |
| Data egress & transfer fees | Rarely | ✓ High impact |
| Third-party software licensing | Sometimes | ✓ Often underestimated |
| Observability & monitoring | Rarely | ✓ Grows with scale |
| Internal engineering time | Rarely | ✓ Largest hidden cost |
| Unused Reserved Instances | No | ✓ Common waste driver |
3 Treating Security & Compliance as an Afterthought
The shared responsibility model is one of the most frequently misunderstood frameworks in cloud computing. Cloud providers secure the infrastructure; customers are responsible for everything built on top of it - including identity management, data encryption, network configurations, and application-layer controls. Organizations that assume 'the cloud provider handles security' discover this boundary painfully when a misconfigured S3 bucket or an overly permissive IAM role becomes a breach vector.
The exposure risk: IBM's Cost of a Data Breach report consistently identifies misconfiguration as one of the leading causes of cloud-related security incidents - with average breach costs now exceeding $4.4 million per incident globally.
Compliance adds a further dimension. Regulated industries - financial services, healthcare, government contractors - operate under frameworks (PCI-DSS, HIPAA, SOC 2, ISO 27001) that carry specific technical controls. Retrofitting compliance into a cloud environment after migration is materially more expensive than designing for it at the architecture stage.
The fix: Embed a 'security by design' posture into the cloud landing zone before a single production workload migrates. Implement cloud security posture management (CSPM) tooling, enforce least-privilege IAM policies, enable encryption at rest and in transit by default, and map applicable compliance frameworks to your cloud architecture during the design phase - not after go-live.
4 Migrating Without a Cloud Governance Framework
Cloud agility is a double-edged capability. The same self-service provisioning that enables development teams to spin up environments in minutes also enables unconstrained resource sprawl, inconsistent tagging, shadow IT proliferation, and configuration drift. Without governance guardrails in place from day one, organizations accumulate cloud debt as quickly as they accumulate cloud resources.
Common governance gaps: No resource tagging standards, no cost allocation by team or product line, no policy enforcement for region selection, no automated alerting on anomalous spend, and no formal decommissioning process for test environments.
Governance failures compound over time. A six-month-old cloud environment without tagging standards is nearly impossible to retrospectively tag accurately. Orphaned resources - dev environments from completed projects, snapshots from decommissioned servers - accumulate silently and appear only when a cloud audit surfaces the bill.
The fix: Establish a Cloud Center of Excellence (CCoE) before migration begins. Define mandatory tagging taxonomies, cost allocation structures, policy-as-code enforcement (AWS Service Control Policies, Azure Policy, GCP Organization Policies), and a regular cloud hygiene review cycle. Make governance a prerequisite for any team onboarding to the cloud - not an optional layer added later.
5 Migrating Without Robust Testing & Rollback Plans
Speed pressure is the enemy of resilience in cloud migrations. When executive stakeholders are watching a project timeline, engineering teams face implicit pressure to compress testing cycles. The result is production migrations that expose defects - performance degradation, integration failures, data integrity issues - that would have been caught in a staging environment.
The operational risk: Downtime during a failed migration cutover is not just a technology problem. For every hour of unexpected production outage, the business impact includes direct revenue loss, customer trust erosion, SLA penalty exposure, and the engineering cost of an unplanned incident response cycle.
Equally critical - and equally overlooked - is the rollback plan. Most migration teams design a forward path in detail and a reverse path in outline. When a cutover fails, the absence of a documented, tested rollback procedure turns a recoverable incident into an extended outage.
The fix: Treat every cloud migration as a release deployment. Require full integration and performance testing in a cloud staging environment that mirrors production topology. Define explicit go/no-go criteria for cutover decisions. Document and test rollback procedures - not just document them. For critical workloads, adopt blue/green or canary deployment patterns to reduce blast radius during initial traffic cutover.
Action checklist
- Load-test migrated services at 120-150% of expected peak load in staging
- Define measurable go/no-go cutover criteria (error rate, p99 latency, throughput)
- Conduct a full rollback rehearsal at least once before production cutover
- Establish a hypercare period of 2-4 weeks post-migration with enhanced monitoring
The Compounding Cost of Getting It Wrong
Each of the five mistakes above carries an individual cost. But the real danger is compounding: an organization that lifts and shifts without optimization, builds no governance framework, skips pre-migration security design, and cuts testing short is not making five mistakes - it is building a system where each failure amplifies the others.
The organizations that execute cloud migrations successfully are not the ones with the largest budgets. They are the ones that invest in the upfront rigor - workload rationalization, TCO modeling, security architecture, governance policy, and testing discipline - that prevents the expensive rework cycles that dominate failed migrations.
Key Takeaways
- Apply the 6R framework to every workload before migration - lift-and-shift should be the exception, not the default
- Build a full TCO model that includes egress, licensing, observability, and people costs
- Design your cloud security posture and compliance architecture before migration, not after
- Establish a Cloud Center of Excellence with tagging standards and policy enforcement on day one
- Require staging-environment testing and documented rollback procedures for every production cutover
Ready to De-Risk Your Cloud Migration?
Explore our full library of cloud strategy resources, migration frameworks, and expert guides - built for enterprise IT and operations leaders.
Contact Us →- Zero Trust Security for Modern Enterprises April 28, 2026
- How to Avoid the 5 Most Common Cloud Migration Mistakes April 14, 2026
- Edge Computing and 5G-Plus: A Powerful Combination February 5, 2026
- H-1B Visa Explained: Everything You Need to Know in 2026 January 12, 2026
- Top Quantum Programming Languages You Should Learn in 2026 December 10, 2025
